Daily
Protocolometer
Evaluate your daily use of protocols!Did you use a computer or smartphone today to connect to the Internet (e.g. surf the web, check your emails, play online games, stream music, etc...)?
When connecting to the Internet, you are transferring data between computers using the TCP/IP range of protocols.
These protocols rely on packet switching and the use of IP addresses to uniquely identify each device on the network.
These protocols rely on packet switching and the use of IP addresses to uniquely identify each device on the network.

Did you access any website today, using a web browser such as Google Chrome, Microsoft Edge or Safari?
Web browsers such as Google Chrome or Safari use the HTTP and the HTTPS protocols to access webpages.
HTTP stands for HyperText Transfer Protocol and requires web pages to be coded using the HTML language.
HTTP stands for HyperText Transfer Protocol and requires web pages to be coded using the HTML language.

Did you check your email inbox today?
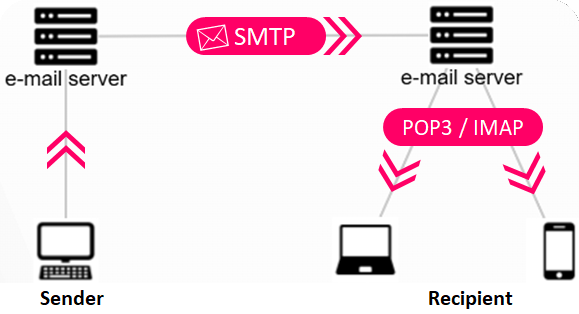
When accessing/retrieving emails from an email server you can use either the POP3 protocol or the IMAP protocol.
The Post-Office Protocol (e.g. POP3) means that when you retrieve an email from your mail server, this email is downloaded to your computer (client) and is removed from the mail server (to free up space on your mail server). The drawback of this protocol is that, if later on you check your emails again using a different device (e.g. smartphone, tablet, laptop, etc.) then you will not be able to retrieve this email again as it is no longer on the mail server.
The IMAP protocol does address this issue. It means that when accessing your emails, these emails remain on the mail server. The same emails can hence be accessed many times from multiple devices. Be careful though, as you will need to delete these emails from time to time to make space on your mail server.
The Post-Office Protocol (e.g. POP3) means that when you retrieve an email from your mail server, this email is downloaded to your computer (client) and is removed from the mail server (to free up space on your mail server). The drawback of this protocol is that, if later on you check your emails again using a different device (e.g. smartphone, tablet, laptop, etc.) then you will not be able to retrieve this email again as it is no longer on the mail server.
The IMAP protocol does address this issue. It means that when accessing your emails, these emails remain on the mail server. The same emails can hence be accessed many times from multiple devices. Be careful though, as you will need to delete these emails from time to time to make space on your mail server.
Did you send any email today?
When you compose an email and press the send button, this email is uploaded to the outbox of your email server. It is then automatically sent from your email server to the email server of the recipient using the SMTP protocol.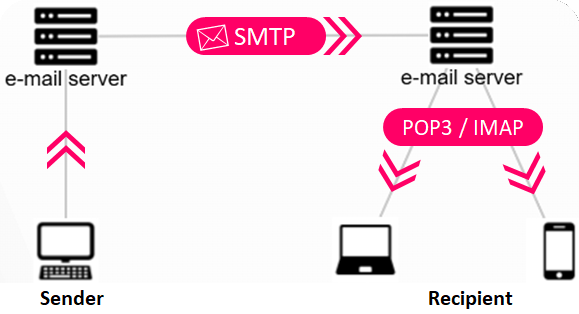
Did you transfer files today between two devices without using a website or an email?
There is a range of protocols for transferring files between devices or computers on a network.
Some of these protocols are proprietary protocols such as the AirDrop protocol from Apple.
However, over a network such as the Internet, it is preferable to use standard protocols as these will be compatible between many different devices produced by different manufacturers.
The FTP (File Transfer Protocol) is a standard protocol for transferring files between two computers. A web developer might use the FTP protocol for instance to transfer (upload) all the files of a website from their computer to the web server where the website will be hosted. They can also use the FTP protocol to take a backup of all the files that are on their server to back them up on their own computer. To use the FTP protocol they will need to install an FTP client utility such as FileZilla.
Some of these protocols are proprietary protocols such as the AirDrop protocol from Apple.
However, over a network such as the Internet, it is preferable to use standard protocols as these will be compatible between many different devices produced by different manufacturers.
The FTP (File Transfer Protocol) is a standard protocol for transferring files between two computers. A web developer might use the FTP protocol for instance to transfer (upload) all the files of a website from their computer to the web server where the website will be hosted. They can also use the FTP protocol to take a backup of all the files that are on their server to back them up on their own computer. To use the FTP protocol they will need to install an FTP client utility such as FileZilla.
Did you access online content using your smartphone from home?
When accessing the Internet from home using a laptop, smartphone, or tablet, it is recommended to connect to your home network using the WiFi.
WiFi protocols enable devices to connect to a Local Area Network wirelessly, through radio waves. Your device connects to a Wireless hub called a WAP (Wireless Access Point).
As radio waves can easily be intercepted by anyone in proximity of the Wireless Access Point, it is highly recommended to use an encription key (wifi key) to encrypt all wireless communication.
WiFi protocols enable devices to connect to a Local Area Network wirelessly, through radio waves. Your device connects to a Wireless hub called a WAP (Wireless Access Point).

As radio waves can easily be intercepted by anyone in proximity of the Wireless Access Point, it is highly recommended to use an encription key (wifi key) to encrypt all wireless communication.
Did you access online content using your smartphone while on the move (e.g. commuting to school/work)?
WiFi protocols are only available when you are within range of a WiFi hotspot. (e.g. at home, in school, in a restaurant or hotel, etc.). You can still access the Internet while on the move, but in this case you will most likely be using 3G/4G or the most recent 5G protocols.

Did you use a desktop computer, game console or smart TV today?
If you are accessing your school network or home network from a fixed computer (desktop, game console, smartTV), it is very likely that this device will be connected to a network switch or hub using an Ethernet cable.
On your way to school, did you use wireless headphones or earphones connected to your smartphone?
Wireless headphones or earphones use the Bluetooth protocol to connect a wireless device to your phone/computer.
The End!